防SQL注入的php类库
- 作者: 五速梦信息网
- 时间: 2026年03月19日 18:00
防SQL注入的php类库
<?php
class sqlsafe {
private \(getfilter = "'|(and|or)\\b.+?(>|<|=|in|like)|\\/\\*.+?\\*\\/|<\\s*script\\b|\\bEXEC\\b|UNION.+?SELECT|UPDATE.+?SET|INSERT\\s+INTO.+?VALUES|(SELECT|DELETE).+?FROM|(CREATE|ALTER|DROP|TRUNCATE)\\s+(TABLE|DATABASE)";
private \)postfilter = “\b(and|or)\b.{1,6}?(=|>|<|\bin\b|\blike\b)|\/\*.+?\*\/|<\s*script\b|\bEXEC\b|UNION.+?SELECT|UPDATE.+?SET|INSERT\s+INTO.+?VALUES|(SELECT|DELETE).+?FROM|(CREATE|ALTER|DROP|TRUNCATE)\s+(TABLE|DATABASE)”;
private \(cookiefilter = "\\b(and|or)\\b.{1,6}?(=|>|<|\\bin\\b|\\blike\\b)|\\/\\*.+?\\*\\/|<\\s*script\\b|\\bEXEC\\b|UNION.+?SELECT|UPDATE.+?SET|INSERT\\s+INTO.+?VALUES|(SELECT|DELETE).+?FROM|(CREATE|ALTER|DROP|TRUNCATE)\\s+(TABLE|DATABASE)";
public function __construct() {
foreach(\)_GET as \(key=>\)value){\(this->stopattack(\)key,\(value,\)this->getfilter);}
foreach(\(_POST as \)key=>\(value){\)this->stopattack(\(key,\)value,\(this->postfilter);}
foreach(\)_COOKIE as \(key=>\)value){\(this->stopattack(\)key,\(value,\)this->cookiefilter);}
}
public function stopattack(\(StrFiltKey, \)StrFiltValue, \(ArrFiltReq){
if(is_array(\)StrFiltValue))\(StrFiltValue = implode(\)StrFiltValue);
if (preg_match(“/”.\(ArrFiltReq."/is",\)StrFiltValue) == 1){
\(this->writeslog(\)_SERVER[“REMOTE_ADDR”].“ ”.strftime(“%Y-%m-%d %H:%M:%S”).“ ”.\(_SERVER["PHP_SELF"]." ".\)_SERVER[“REQUEST_METHOD”].“ ”.\(StrFiltKey." ".\)StrFiltValue);
showmsg(‘您提交的参数非法,系统已记录您的本次操作!’,‘’,0,1);
}
}
public function writeslog(\(log){
\)log_path = CACHE_PATH.‘logs’.DIRECTORY_SEPARATOR.‘sql_log.txt’;
\(ts = fopen(\)log_path,“a+”);
fputs(\(ts,\)log.“\r\n”);
fclose($ts);
}
}相关文章
-
phpmailer的使用详细方法与示例 用腾讯的邮箱帐号发送邮件
phpmailer的使用详细方法与示例 用腾讯的邮箱帐号发送邮件
- 技术栈
- 2026年03月19日
-
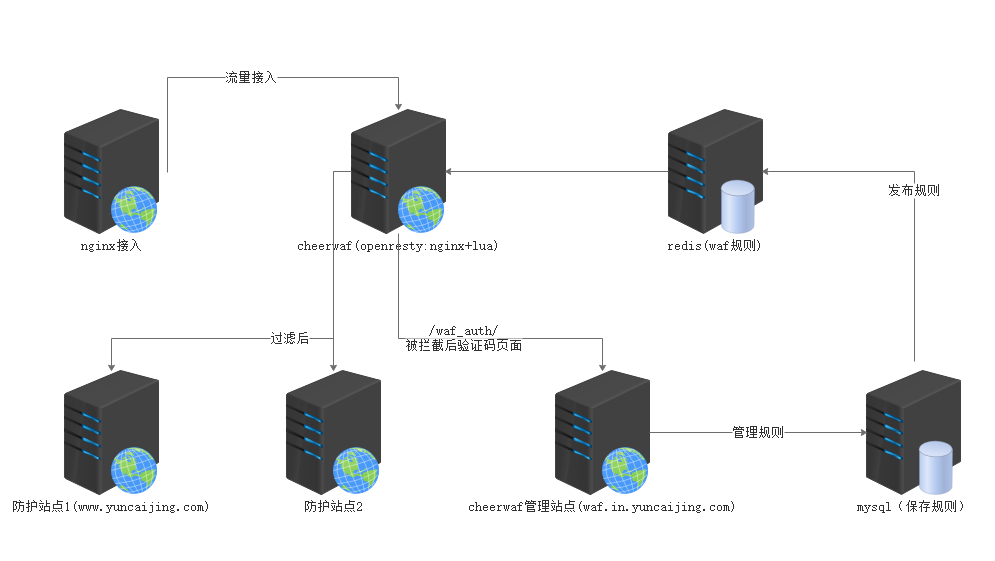
基于 openresty 的 web 应用防火墙 cheerwaf
基于 openresty 的 web 应用防火墙 cheerwaf
- 技术栈
- 2026年03月19日
-
编辑器或评论留言里面可以粘贴上传图片
编辑器或评论留言里面可以粘贴上传图片
- 技术栈
- 2026年03月19日
-
简单token验证php程序小实例
简单token验证php程序小实例
- 技术栈
- 2026年03月19日
-
当才华支撑不住你的野心,你就应该静下心来读书学习
当才华支撑不住你的野心,你就应该静下心来读书学习
- 技术栈
- 2026年03月19日
-

Token有什么作用?又是什么原理呢
Token有什么作用?又是什么原理呢
- 技术栈
- 2026年03月19日
